Can hackers Shut Down a Power Grid? Cyber Warfare Explained

Can Hackers Shut Down a Country’s Power Grid? The Science of Cyber Warfare
Electricity powers everything from hospitals to stock markets, making the power grid the lifeline of modern society. But what if that lifeline could be severed not by physical force, but by lines of code? Cyber warfare has emerged as a stealthy threat, capable of plunging nations into darkness. In this deep dive, we'll explore whether hackers can truly shut down a country's power grid, dissect how such attacks unfold, and examine why grids have become prime targets in digital conflicts.
What Is a Power Grid and Why Is It Vulnerable?
A power grid is an intricate network that includes power plants, high-voltage transmission lines, substations, transformers, and control centers. To manage this complexity, operators use industrial control systems (ICS) and SCADA (Supervisory Control and Data Acquisition) systems—technologies designed in the pre-internet era for efficiency, not security.
The Core Vulnerabilities
Many grids suffer from inherent weaknesses:
- Outdated Software and Hardware: Legacy systems running on Windows XP or older can't receive security patches.
- Weak Encryption and Connectivity: Some components connect to the internet or corporate networks, creating entry points for attackers.
- Human Factors: Phishing and insider threats exploit the weakest link—people.
According to the U.S. Department of Energy, these flaws make grids "attractive targets for adversaries with advanced cyber capabilities" (source: DOE Cybersecurity Report).
How Can Hackers Attack a Power Grid?
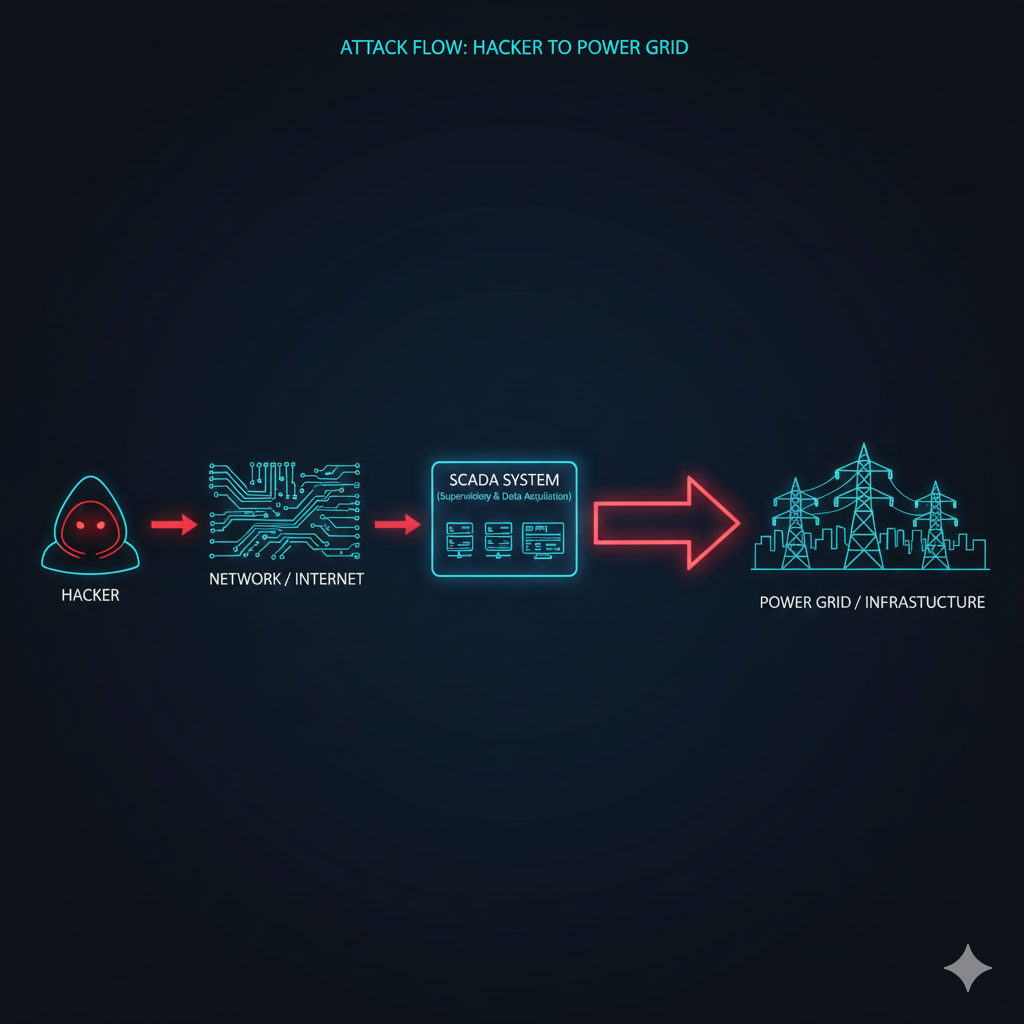
Disrupting a grid isn't trivial—it requires precision and persistence—but it's feasible. Attacks often follow a multi-stage process, akin to military operations.
1. Initial Access
Attackers breach defenses via:
- Phishing emails targeting employees.
- Stolen credentials or infected USBs.
- Supply chain compromises, like malware in vendor software.
2. Lateral Movement and Reconnaissance
Once inside, hackers navigate networks to:
- Locate SCADA systems and map grid layouts.
- Study operational protocols without alerting defenders.
3. Command Execution and Disruption
At this point, attackers can:
- Manipulate circuit breakers to cause overloads.
- Disable safety mechanisms, leading to cascading failures.
- Trigger blackouts that ripple across regions.
This phase can blackout areas in minutes, as seen in documented cases.
Real-World Cyber Attacks on Power Grids

Ukraine Power Grid Attacks (2015 and 2016)
Russian-linked hackers (attributed to groups like Sandworm) infiltrated Ukrainian utilities, remotely disabling substations. In 2015, 230,000 people lost power for hours; the 2016 attack lasted longer, locking operators out while malware executed commands. These incidents, detailed in reports from the Electric Power Research Institute (EPRI), showed how SCADA systems could be weaponized.
Stuxnet (2010)
Though targeting Iran's nuclear program, Stuxnet—a U.S.-Israel collaboration—proved malware could sabotage physical infrastructure. It altered centrifuge speeds, causing equipment failure, and highlighted the potential for cyber tools to inflict tangible damage.
Recent Incidents
In 2022, a cyber attack disrupted India's power grid in Rajasthan, affecting millions. Experts link it to state actors, underscoring the growing trend (source: Reuters).
Who Is Capable of Such Attacks?
Grid takeovers aren't solo endeavors. They demand:
- Expertise in ICS protocols.
- Intelligence on targets.
- Resources for prolonged operations.
Primary actors are nation-states, such as Russia's GRU or China's PLA cyber units, often operating under state sponsorship. Non-state groups like hacktivists lack the scale, but insider threats or rogue actors could pose risks.
Could an Entire Country Be Shut Down?
A total nationwide blackout is challenging due to grid segmentation, redundancies, and manual overrides. However, targeted strikes can cripple key areas. For instance, attackers might focus on urban centers during heatwaves, amplifying chaos. The 2015 Ukraine attack caused localized outages but didn't collapse the whole system—yet it disrupted 10% of the country's power.
Potential scenarios include:
- Coordinated hits on multiple regions.
- Hybrid attacks combining cyber with physical sabotage.
- Long-term damage, like fried transformers that take months to replace.
Why Power Grids Are Strategic Targets
Grids offer asymmetric advantages:
- High Impact: Outages affect millions, causing economic losses (e.g., $1 billion per day in the U.S., per DHS estimates).
- Rapid Spread: Failures cascade like dominos.
- Denial and Attribution: Attacks are hard to trace, allowing plausible deniability.
In cyber warfare, grids are "soft targets" that maximize disruption with minimal risk.
How Countries Defend Their Power Grids

Defenses are evolving but face hurdles:
- Network Segmentation: Isolates critical systems.
- Zero-Trust Models: Verifies every access request.
- Offline Backups and Simulations: Red-team exercises test vulnerabilities.
- AI and Monitoring: Detects anomalies in real-time.
However, upgrades are costly—U.S. utilities spend billions annually—and uneven globally. Developing nations lag behind, per the International Energy Agency (IEA).
The Future of Cyber Warfare
Emerging threats include:
- AI-Powered Malware: Self-learning attacks that adapt.
- Autonomous Chains: Fully automated intrusions.
- Hybrid Warfare: Cyber fused with drones or EMPs.
- Multi-Infrastructure Attacks: Targeting grids alongside water or telecom.
As grids integrate renewables and IoT, vulnerabilities may increase. For more on this, check our guide to smart grid risks.
FAQs
- Can a single hacker shut down a power grid? Unlikely. It requires teams, funding, and expertise—typically state-backed.
- Are power grids directly connected to the internet? Not always directly, but indirect links via vendors or remote access create risks.
- Can outages be permanent? Equipment like transformers can take months to repair, enabling prolonged disruptions.
- Is cyber warfare against grids legal? International law lags; the Tallinn Manual classifies some as acts of war.
- How common are these attacks? Incidents have risen—over 200 reported globally since 2010, per cybersecurity firms like Dragos.
Resources & Further Reading
- IEA: Power System Security and Resilience
- U.S. DOE: Cybersecurity for Energy Delivery Systems
- MIT Technology Review: Cyber Attacks on Critical Infrastructure
- NIST: Cybersecurity Framework for ICS
- ENISA: Threat Landscape for Critical Infrastructure
Final Thoughts
The era of cyber warfare has arrived, turning code into a weapon of mass disruption. Power grids, once seen as untouchable, are now battlegrounds. While defenses are strengthening, the threat persists—especially for unprepared nations. The next major blackout might not be a storm; it could be a digital assault.
What do you think—is cyber warfare deadlier than conventional arms? Share your views in the comments or explore more on our blog.
Comments